Developer of Checkm8 explains why iDevice jailbreak exploit is a game changer
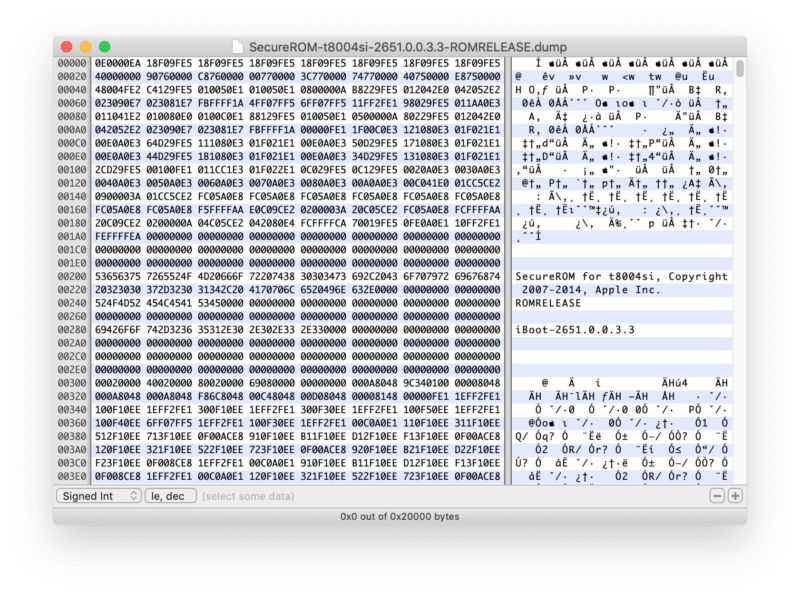
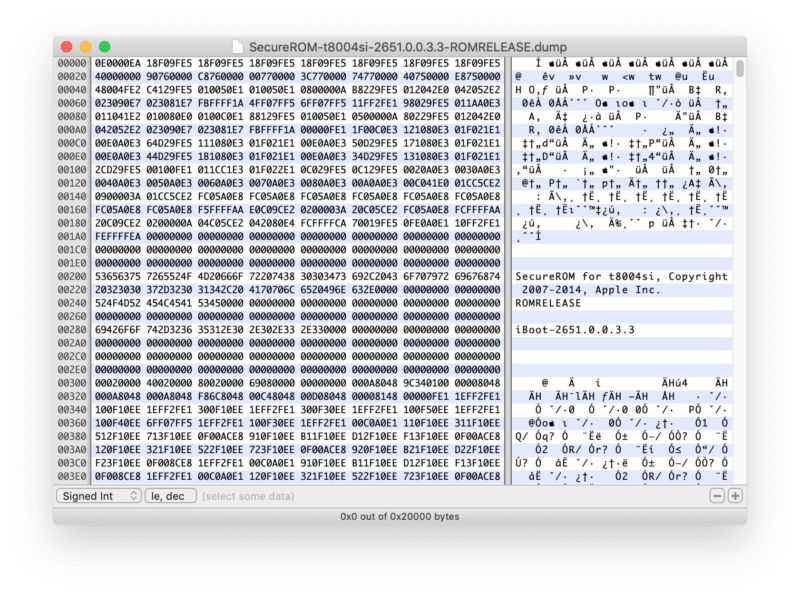
Enlarge / The bootrom of an Apple Watch Series 3, as shown through a hex viewer. Yep, Apple Watches series 1, 2, and 3 are also vulnerable to Checkm8.
Often, when new iOS jailbreaks become public, the event is bitter-sweet. The exploit allowing people to bypass restrictions Apple puts into the mobile operating system allows hobbyists and researchers to customize their devices and gain valuable insights be peeking under the covers. That benefit is countered by the threat that the same jailbreak will give hackers a new way to install malware or unlock iPhones that are lost, stolen, or confiscated by unscrupulous authorities.
On Friday, came the release of Checkm8. Unlike just about every jailbreak exploit released in the past nine years, it targets the iOS bootrom, which contains the very first code that’s executed when an iDevice is turned on. Because the bootrom is contained in read-only memory inside a chip, jailbreak vulnerabilities that reside here can’t be patched.
Checkm8 was developed by a hacker who uses the handle axi0mX. He’s the developer of another jailbreak-enabling exploit called alloc8 that was released in 2017. Because it was the first known iOS bootrom exploit in seven years, it was of intense interest to researchers, but it worked only on the iPhone 3GS, which was seven years old by the time alloc8 went public. The limitation gave the exploit little practical application.
Comments
Post a Comment